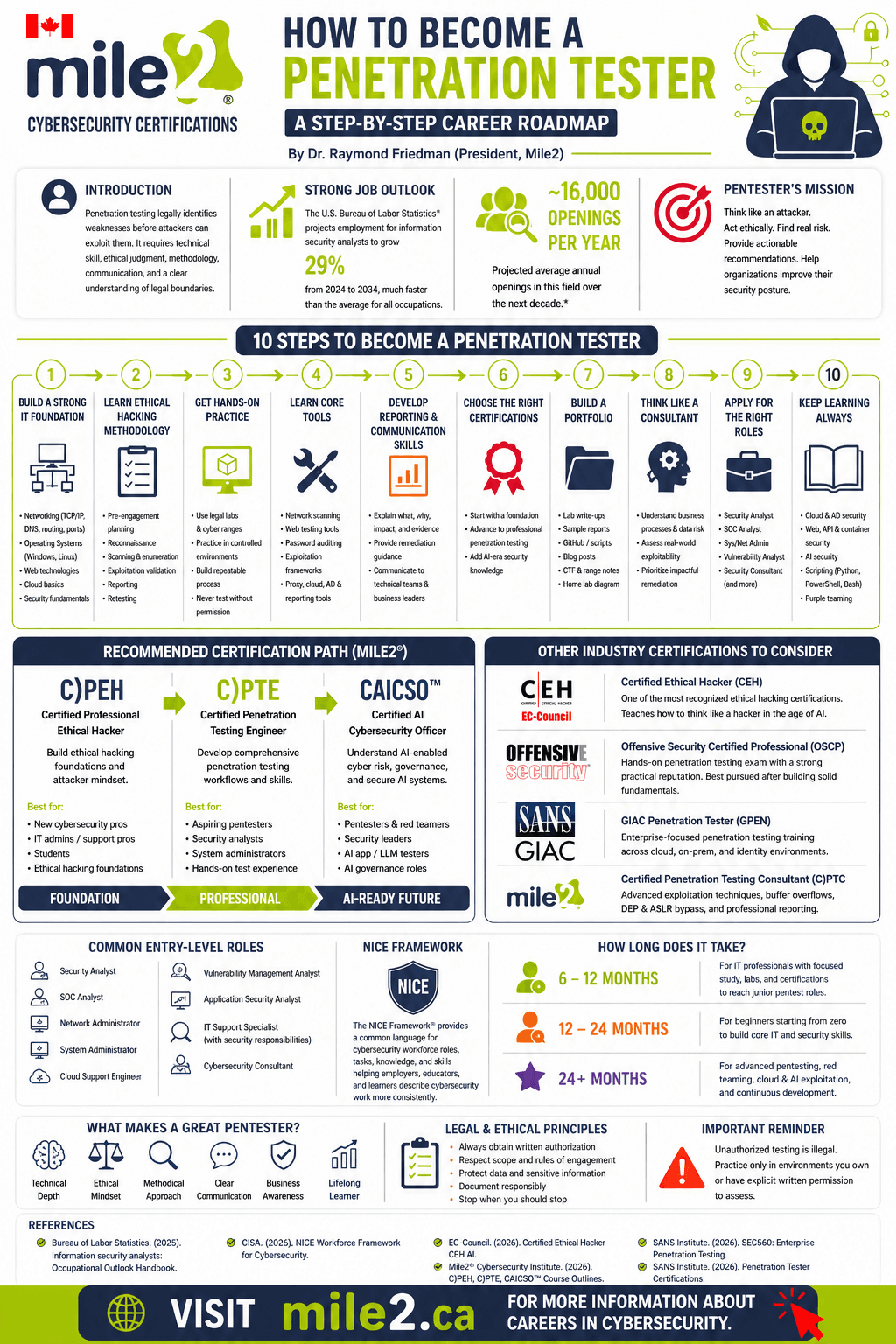
How to Become a Penetration Tester: A Step-by-Step Career Roadmap [infographics]
Penetration testing is one of the most practical career paths in cybersecurity. A penetration tester, often called a pen tester, pentester, or ethical hacker, is hired to test systems, networks, cloud environments, applications, and organizations for weaknesses before real attackers exploit them.
Download as PDF
For many learners, penetration testing feels like the hands-on side of cybersecurity. It includes reconnaissance, vulnerability discovery, exploitation validation, reporting, and helping organizations reduce risk.
But professional penetration testing is not only about tools.
It requires technical skill, ethical judgment, structured methodology, legal awareness, and clear communication.
In Canada, this work matters across government, finance, healthcare, education, energy, and small business. The Canadian Centre for Cyber Security encourages organizations to apply practical baseline controls to reduce common cyber risks, especially for small and medium-sized organizations.
The U.S. Bureau of Labor Statistics projects employment for information security analysts to grow 29 percent from 2024 to 2034, much faster than average. This category is broader than penetration testing, but it reflects steady demand for professionals who protect networks and systems.
This roadmap explains how to become a penetration tester and how Mile2 certifications fit into the path.
A strong Mile2 progression looks like this:
Certified Security Principles C)SP →
Certified Professional Ethical Hacker C)PEH →
Certified Penetration Testing Engineer C)PTE →
Certified AI Cybersecurity Officer C)AICSO
What Does a Penetration Tester Do?
A penetration tester evaluates security by thinking like an attacker while working under written authorization.
The goal is not to “break in” for attention.
The goal is to identify weaknesses, prove real-world risk, and give the organization clear steps to reduce exposure.
A professional penetration test often includes:
- Reconnaissance, scanning, enumeration, vulnerability validation, controlled exploitation, and evidence collection.
- Web application testing, password testing, Active Directory testing, cloud review, wireless testing, and report writing.
- Business risk communication, remediation guidance, and retesting.
The best pentesters are not tool operators.
They understand how systems work. They understand how attackers chain weaknesses together. They explain risk to technical teams, executives, and compliance staff.
Step 1: Build a Strong IT Foundation
Before exploitation techniques, you need the systems knowledge behind the target.
Start with networking, operating systems, security fundamentals, web technologies, and cloud basics.
If you are new to IT, start with Certified IT Principles C)ITP or Certified Network Principles C)NP.
The C)NP course covers TCP/IP, switches, routers, wireless networking, network security, network planning, and day-to-day operations. Mile2 positions C)NP for learners who need practical network knowledge before moving deeper into cybersecurity.
For security fundamentals, Certified Security Principles C)SP is a strong next step. It covers risk management, cryptography, identity and access management, data security, network security, server security, application security, compliance, and auditing.
This foundation helps you understand what you are testing.
A port scan means more when you understand the service behind it.
A web vulnerability means more when you understand authentication, sessions, databases, and input validation.
A cloud misconfiguration means more when you understand identity, storage, logging, and shared responsibility.
Step 2: Learn Ethical Hacking Methodology
A professional pentest follows a process.
This separates real penetration testing from random scanning.
A typical methodology includes:
- Pre-engagement planning
- Scope and rules of engagement
- Reconnaissance
- Scanning and enumeration
- Vulnerability analysis
- Exploitation validation
- Post-exploitation analysis
- Reporting
- Remediation support
- Retesting
Many beginners skip the first two steps.
That creates risk.
A professional pentester needs to know what is authorized, what is out of scope, what systems require extra care, what testing windows apply, and when to stop.
The Certified Professional Ethical Hacker C)PEH course is Mile2’s foundation for penetration testing. Mile2 describes C)PEH as foundational training in its penetration testing line because it teaches learners to see systems through the eyes of an attacker.
The course includes ethical hacking, Linux fundamentals, protocols, cryptography, password cracking, malware, passive reconnaissance, active reconnaissance, vulnerability assessment, network attacks, server attacks, web technologies, wireless, and maintaining access.
Step 3: Practice in Legal Lab Environments
Penetration testing is a practical skill.
Reading helps. Labs build capability.
Use legal cyber ranges, vulnerable virtual machines, CTF-style practice, and structured training labs.
Focus on process, not tricks.
Good practice areas include scanning a lab network, identifying live hosts, enumerating services, researching vulnerabilities, testing weak credentials, writing findings, and creating remediation steps.
Never test systems you do not own or systems where you lack written permission.
In Canada, unauthorized testing creates legal and professional risk. Your intent does not replace permission.
Step 4: Learn the Core Tools
Tools matter.
Tool dependence creates weak testers.
A strong pentester understands what each tool does, why the output matters, and how to validate the result manually.
Common tool categories include network scanners, web proxies, password auditing tools, directory discovery tools, exploitation frameworks used in labs, cloud assessment tools, Active Directory assessment tools, and reporting platforms.
Mile2’s Certified Penetration Testing Engineer C)PTE builds on ethical hacking and moves into structured testing.
The C)PTE course focuses on five key elements of penetration testing: information gathering, scanning, enumeration, exploitation, and reporting. It also includes hands-on labs in reporting tools, information gathering, live system detection, enumeration, vulnerability assessment, Windows system hacking, exploitation, PowerShell, network sniffing, and web application attacks.
Step 5: Learn Web Application Security
Many modern attacks start with web applications, APIs, authentication flows, and business logic weaknesses.
A penetration tester needs to understand HTTP, HTTPS, cookies, sessions, access control, databases, JavaScript, APIs, input validation, and common web attack patterns.
For learners focused on application security, Certified Secure Web Application Engineer C)SWAE is a useful addition.
The C)SWAE course includes secure SDLC, OWASP Top 10, risk management, threat modelling, authentication and authorization attacks, session management, data validation, code review, application mapping, cryptography, and web application penetration testing.
For external reference, the OWASP Top 10 remains a respected starting point for understanding common web application security risks. It also helps developers and testers use shared language when discussing web vulnerabilities.
Step 6: Build Reporting and Communication Skills
A pentest report is often the most valuable deliverable.
A good report explains what was tested, what was found, why it matters, what evidence supports the finding, and what to fix first.
Executives need business impact.
Administrators need technical detail.
Developers need clear remediation guidance.
Compliance teams need evidence tied to controls.
The job is not finished when a vulnerability is confirmed.
The job is finished when the organization understands the risk and knows what action to take.
C)PTE includes report writing basics and reporting labs, which matters because technical findings lose value when stakeholders cannot act on them.
Step 7: Choose the Right Mile2 Certification Path
Your certification path should match your starting point.
If you are new to IT, begin with foundation courses.
If you already work in IT, move toward ethical hacking and penetration testing.
A practical Mile2 path
C)NP Certified Network Principles
Best for learners who need networking fundamentals.
C)SP Certified Security Principles
Best for learners building security fundamentals across risk, access, network security, server security, application security, and compliance.
C)PEH Certified Professional Ethical Hacker
Best for learners entering ethical hacking and attacker-style thinking.
C)PTE Certified Penetration Testing Engineer
Best for learners moving into professional penetration testing workflows.
C)PTC Certified Penetration Testing Consultant
Best for advanced learners who want deeper exploitation, team-based pentesting, buffer overflow concepts, and advanced report writing.
C)AICSO Certified AI Cybersecurity Officer
Best for professionals preparing for AI security risk, AI governance, GenAI security, AI red teaming, and secure AI adoption.
Step 8: Add Canadian Context to Your Career Plan
Canadian employers need professionals who understand risk, privacy, critical services, cloud adoption, and incident response.
The Canadian Centre for Cyber Security’s baseline controls guide gives small and medium-sized organizations practical controls to reduce common cyber risk. This is useful reading for aspiring pentesters because it shows how testing connects to real defensive priorities.
The Canadian Cyber Security Skills Framework also links cybersecurity work to workforce roles and skills. It references the NICE Framework as a way to describe cybersecurity work, including technical and non-technical roles.
This matters because “penetration tester” is not the only title in job postings.
You might also see:
- Security consultant
- Offensive security analyst
- Vulnerability assessment analyst
- Application security analyst
- Red team operator
- Cybersecurity analyst
- Security engineer
- Cloud security analyst
Use the role description, not only the title.
Step 9: Build a Safe Portfolio
Employers want proof of skill.
A portfolio helps, especially when moving from IT support, networking, school, or system administration into security.
A good beginner portfolio includes lab write-ups, sample pentest reports, safe scripts, blog posts, home lab diagrams, and vulnerability analysis based on intentionally vulnerable systems.
Do not publish real client findings.
Do not publish stolen data.
Do not publish exploit steps against live systems.
Keep your portfolio professional, legal, and useful.
Step 10: Learn How to Think Like a Consultant
A pentester helps an organization make better security decisions.
That means asking better questions:
- What business process does this system support?
- What data is exposed?
- Does the weakness lead to privilege escalation?
- Does it support lateral movement?
- Is the issue exploitable in the real environment?
- What fix gives the most risk reduction?
- What should the organization prioritize first?
This mindset separates a junior tool user from a professional penetration tester.
Step 11: Keep Learning
Penetration testing changes fast.
Cloud platforms, identity systems, SaaS tools, APIs, containers, AI agents, and endpoint defenses keep shifting how testing works.
A modern pentester should keep building skill in cloud security, Active Directory and identity attacks, web application and API testing, container and Kubernetes security, AI security and prompt injection, scripting, detection-aware testing, purple teaming, and professional reporting.
Mile2’s Certified Cloud Security Officer C)CSO also fits this path for professionals testing or defending cloud environments.
The C)CSO course covers cloud risk management, identity and access governance, secure architecture, DevSecOps, AWS, Azure, GCP, legal issues, auditing, compliance, and cloud security operations.
How Long Does It Take to Become a Penetration Tester?
Your timeline depends on your starting point.
Someone already working in IT might move toward junior penetration testing in 6 to 12 months with focused study, labs, certification, and portfolio work.
Someone starting from zero might need 12 to 24 months to build networking, operating system, Linux, Windows, web, cloud, and security fundamentals.
Advanced penetration testing, red teaming, cloud exploitation, and AI-assisted offensive security require longer, ongoing development.
Do not rush the title.
Build competence first.
Final Roadmap
- Learn networking, operating systems, and security fundamentals.
- Study ethical hacking methodology and legal boundaries.
- Practice in legal labs and cyber ranges.
- Learn tools, then validate findings manually.
- Build web, cloud, Linux, Windows, and identity knowledge.
- Earn C)PEH for ethical hacking foundations.
- Advance with C)PTE for professional penetration testing.
- Add C)SWAE for web application security.
- Add C)AICSO for AI-era cybersecurity risk.
- Build a safe portfolio with reports, lab notes, and practical evidence.
References
- Canadian Centre for Cyber Security: Baseline Cyber Security Controls for Small and Medium Organizations
- Canadian Centre for Cyber Security: Canadian Cyber Security Skills Framework
- CISA NICCS: NICE Workforce Framework for Cybersecurity
- U.S. Bureau of Labor Statistics: Information Security Analysts
- OWASP Top 10

